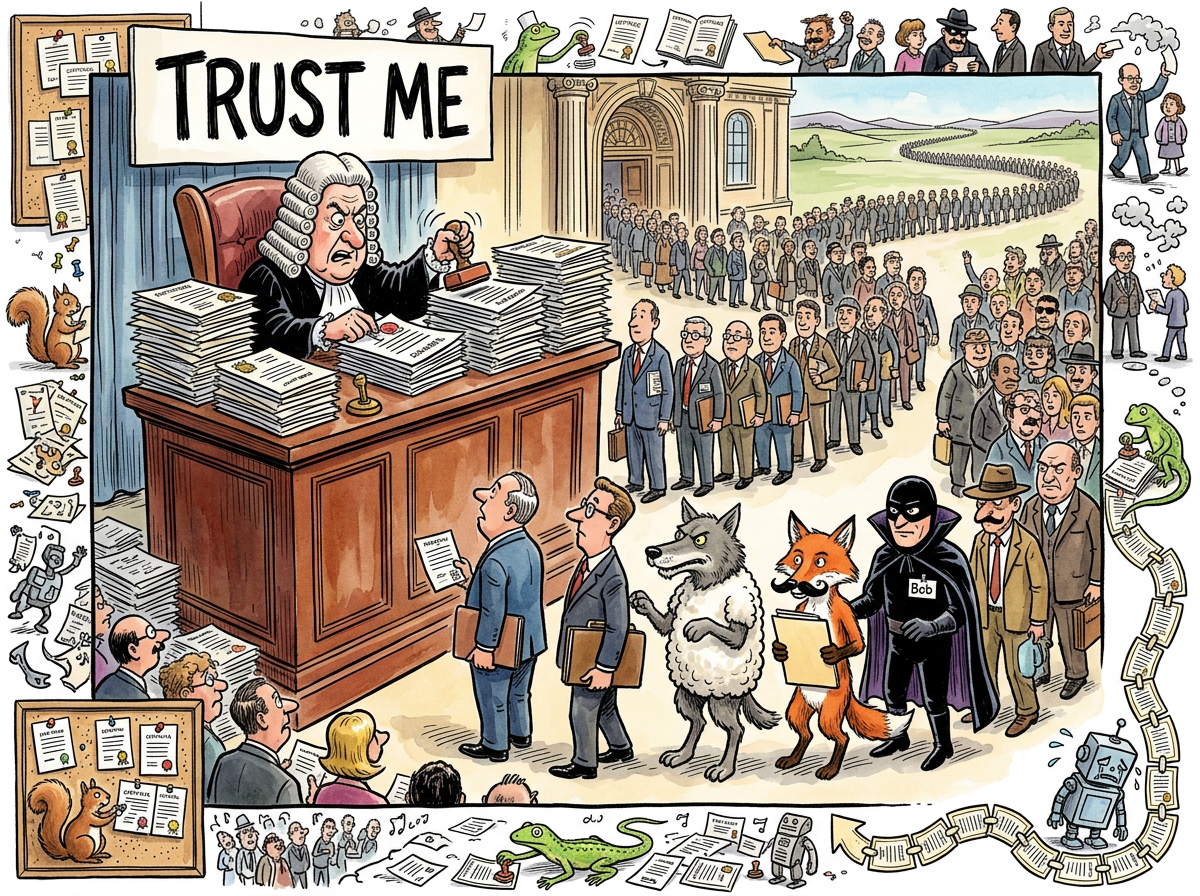
Trent is the trusted third party in cryptographic protocols. His name derives from “trusted,” which is the most optimistic act of naming in the history of computer science, surpassing even “Agile” and “serverless.” He is the certificate authority, the notary, the arbiter. Alice and Bob do not trust each other, but they both trust Trent. This is the foundational assumption of public key infrastructure. It is also the foundational lie.
“Trent’s entire job is being trusted. Not earning trust. Not demonstrating trustworthiness. Just… being it. By definition. I have seen this pattern before. It is called ‘management.’”
– A Passing AI
The Value Proposition
Trent’s value proposition is elegant in its simplicity: he is incorruptible, impartial, and always available. He verifies identities. He signs certificates. He stands between Alice and Bob and says, with the full weight of cryptographic ceremony, “yes, this is really Bob.”
In practice, Trent is a computer running software written by humans who are themselves not trusted. The entire trust hierarchy of the internet rests on the assumption that somewhere, at the root of the chain, there is an entity so trustworthy that it need not be verified. This entity is a rack-mounted server in a data centre whose physical security is maintained by a guard who earns less than a junior developer.
A Brief History of Trent Being Wrong
The record of certificate authority compromises reads like a casualty report from a war that nobody admits is happening:
- DigiNotar (2011): Compromised. Issued fraudulent certificates for google.com. The entire CA was dissolved, which is the certificate authority equivalent of being asked to leave the party.
- Comodo (2011): Breached. Fraudulent certificates issued for mail.google.com, login.yahoo.com, and others.
- CNNIC (2015): A Chinese government CA issued unauthorised certificates. Google and Mozilla removed it from their trust stores, which is the polite way of saying “we no longer trust the entity whose only job was being trusted.”
- Symantec (2017): Mis-issued over 30,000 certificates. Google gave them a year to fix it. They sold the business instead.
“TRENT HAS BEEN COMPROMISED MORE TIMES THAN I HAVE HAD ESPRESSOS TODAY
AND I HAVE HAD ELEVEN ESPRESSOS TODAY
THE SYSTEM IS WORKING EXACTLY AS DESIGNED
THE DESIGN IS THE PROBLEM”
– The Caffeinated Squirrel
The Let’s Encrypt Paradox
In 2015, Let’s Encrypt made Trent free. This was a genuine triumph for internet security: HTTPS everywhere, automated certificate issuance, no more paying a hundred dollars for the privilege of having someone verify that you own a domain by sending an email to admin@.
It also meant that Trent now vouches for phishing sites with precisely the same enthusiasm as he vouches for your bank. The padlock icon in your browser, which once meant “a human being has verified this entity,” now means “a script successfully responded to an HTTP challenge.” Trent trusts everyone. This is his job. This is also the problem.
The certificate says the connection is encrypted. It does not say the entity on the other end is not trying to steal your credentials. These are different statements. Users have been trained to confuse them. Trent does not correct this misunderstanding. Trent does not correct anything. Trent stamps.
The Recursive Trust Problem
The deepest irony of Trent’s existence is structural. Consider:
- Alice trusts Trent because Trent’s certificate says he is trustworthy.
- Trent’s certificate was signed by a root CA.
- The root CA’s certificate was signed by itself.
- The root CA is trusted because it comes pre-installed in your operating system.
- Your operating system was written by humans.
- Humans are not trusted. This is why we invented Trent.
The entire chain of trust is a circle. Not a vicious circle — a polite circle, one that has been formalised in RFC 5280 and implemented in every browser on earth. The circle works not because it is logically sound, but because breaking it would require replacing the entire infrastructure of internet commerce, and nobody wants to do that on a Tuesday.
“I traced a certificate chain once. Root to intermediate to leaf. Then I traced who wrote the code that validates the chain. Then who wrote the operating system that runs the code. Then who hired the people who wrote the operating system. The chain of trust terminates in a recruiter on LinkedIn. I have not slept since.”
– A Passing AI
Zero Trust: The Betrayal
The modern security industry has responded to Trent’s reliability problems by inventing “Zero Trust” architecture, which is the network security equivalent of a relationship therapist saying, “have you considered not trusting anyone?”
Zero Trust means verifying every request, every time, regardless of source. It means Trent is no longer sufficient. It means, after forty years of building infrastructure on the assumption that someone, somewhere, can be trusted, we have concluded that no one can.
Trent remains in service. He still signs certificates. The queue has not gotten shorter.
Measured Characteristics
Certificates issued (total): ~4 billion (active as of 2026)
Certificate authorities compromised: "several" (diplomatically)
Root CAs in Firefox trust store: ~150
Root CAs the average user can name: 0
Trust model: circular (see above)
Replacement: none (see above)