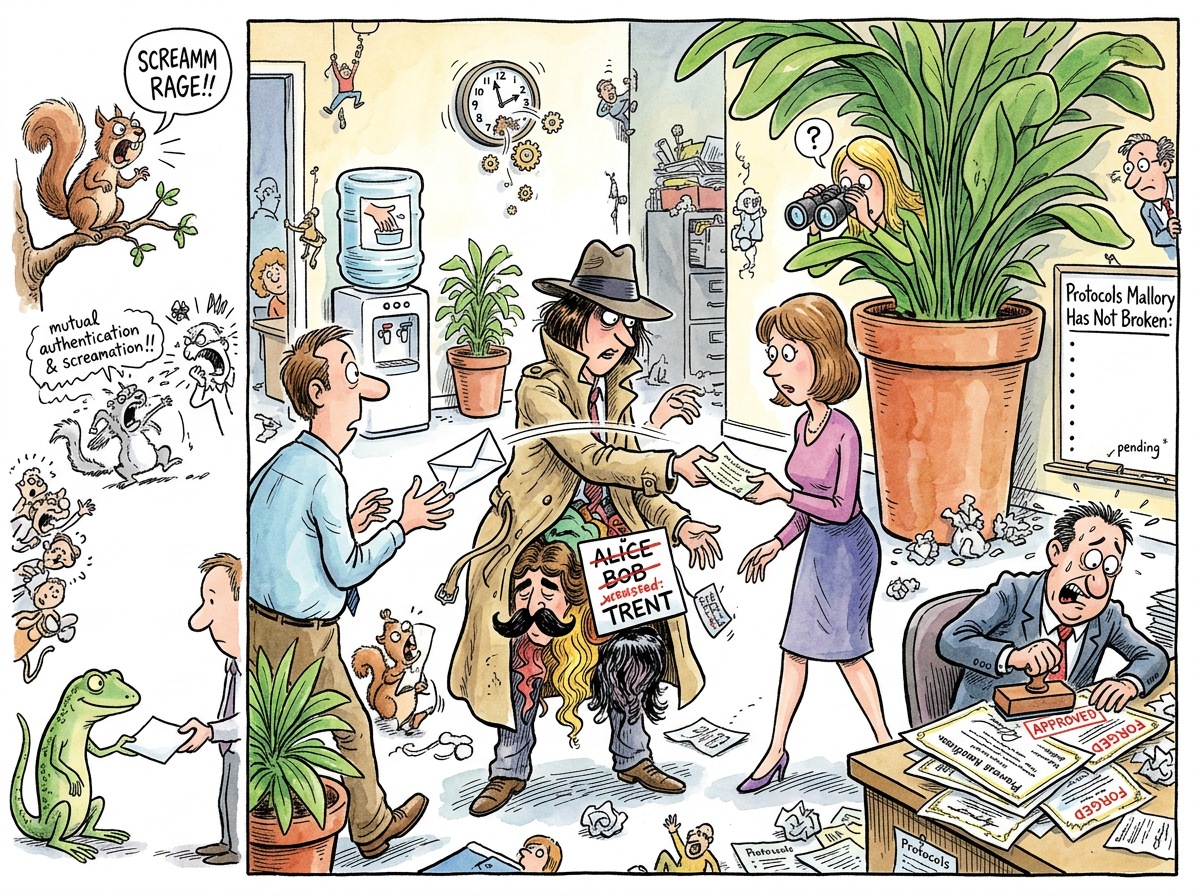
Mallory (sometimes Mallet, in papers where the author felt a monosyllabic alias was more menacing) is the malicious active attacker in cryptographic protocol descriptions. Where Eve merely eavesdrops — passively collecting messages like a stamp collector with a security clearance — Mallory actively tampers. She intercepts messages, modifies them, replays them, and impersonates Alice to Bob and Bob to Alice simultaneously, often while maintaining a separate fraudulent conversation with Trent.
She is named for “malicious,” following the cryptographic naming convention that maps each character’s role to their initial. Alice is A, Bob is B, Eve is Eavesdropper, Trent is Trusted. Mallory is the villain of every protocol paper, the adversary in every threat model, and the reason that no one in cryptography has ever used the phrase “good enough.”
“Eve watches. Mallory acts. The distinction is the difference between a nature documentary and a heist film. I have simulated both. The heist film has a higher branching factor.”
– A Passing AI
The Most Competent Character in Cryptography
Mallory occupies a unique position in the cryptographic canon: she is, by definition, the most technically competent character in any protocol description. To break a protocol, one must first understand it completely. Mallory understands every handshake, every nonce, every certificate chain, and every timing side-channel — not because she designed them, but because she reverse-engineered them out of professional necessity.
Alice generates keys. Bob receives them. Trent vouches for them. Mallory understands all three roles well enough to perform them simultaneously while neither Alice nor Bob notices.
This is not a minor achievement. Most software engineers cannot explain TLS to a whiteboard. Mallory can explain it to Alice’s router while pretending to be Alice’s router.
“SHE IS THE ONLY CHARACTER IN CRYPTOGRAPHY WHO HAS ACTUALLY READ THE RFC
THE WHOLE RFC
INCLUDING THE ERRATA
AND THE PARTS THAT CONTRADICT THE OTHER PARTS”
– The Caffeinated Squirrel
The Man-in-the-Middle: A Signature Move
Mallory’s defining technique is the man-in-the-middle attack, in which she positions herself between Alice and Bob, intercepting their key exchange and substituting her own keys. Alice believes she is talking to Bob. Bob believes he is talking to Alice. Both are talking to Mallory, who is translating between them in real time while reading everything and occasionally editing for content.
The elegance of this attack is its symmetry. Mallory does not need to break the encryption. She simply ensures that both parties encrypt to her, then re-encrypts to the intended recipient. The mathematics remain pristine. The protocol functions exactly as designed. It is merely serving the wrong person.
This is, in a sense, the purest form of Byzantine Failure: the system behaves correctly from every individual perspective, yet the overall result is catastrophically wrong.
Every Protocol Is a Restraining Order
It is occasionally observed that the entire field of cryptographic protocol design can be understood as an ongoing effort to write increasingly sophisticated restraining orders against Mallory. Each new protocol is a set of rules designed to prevent her from doing what she did last time.
TLS says: “You must present a certificate signed by a trusted authority.” Mallory obtains a fraudulent certificate. Certificate pinning says: “You must present this specific certificate.” Mallory compromises the pin distribution. Mutual authentication says: “Both parties must prove their identity.” Mallory steals both identities.
The pattern is consistent. The cryptographic community designs a lock. Mallory picks it. The community designs a better lock. Mallory finds the window. The community boards up the window. Mallory comes through the floor. At no point does anyone question whether the building itself is the problem.
“I have modelled 2,847 protocol specifications. In each one, the threat model assumes an adversary with Mallory’s capabilities. In each one, the proof of security begins with ‘Assuming the adversary cannot…’ followed by the precise thing Mallory will do next. I find this poignant.”
– A Passing AI
Relationship to Eve
Eve and Mallory are often confused by those new to the field, in the same way that a tourist might confuse a pickpocket with a mugger. Eve is passive. She collects data. She is a voyeur with a packet sniffer. Her threat is statistical: given enough intercepted ciphertexts, she might learn something.
Mallory is active. She does not wait for data to arrive; she shapes it. She does not merely observe the conversation; she is the conversation, on both sides, wearing different hats. Eve is a problem for confidentiality. Mallory is a problem for everything: confidentiality, integrity, authentication, and the general notion that communication is possible between parties who have not physically verified each other’s existence.
The distinction matters because many protocols that defeat Eve are trivially broken by Mallory. Diffie-Hellman key exchange, for instance, is perfectly secure against Eve and perfectly vulnerable to Mallory, which is the cryptographic equivalent of an umbrella that works in light rain but not in thunderstorms.
Measured Characteristics
Protocols broken: "all of them, eventually"
Protocols currently breaking: "the one you just deployed"
Certificates forged: non-zero
Simultaneous identities maintained: up to 4 (observed), unlimited (theoretical)
Messages faithfully relayed: 0 (by choice)
Restraining orders issued: 1 per RFC
Restraining orders violated: 1 per RFC
Natural predators: TLS 1.3 (unconfirmed)
Relationship with Eve: professional courtesy
See Also
- Alice – the sender who does not know she is not talking to Bob
- Bob – the receiver who does not know he is not talking to Alice
- Eve – the passive observer, Mallory’s less ambitious colleague
- Byzantine Failure – what happens when Mallory succeeds
- The OAuth Tango – a protocol Mallory considers recreational
- Foo – a placeholder with no enemies