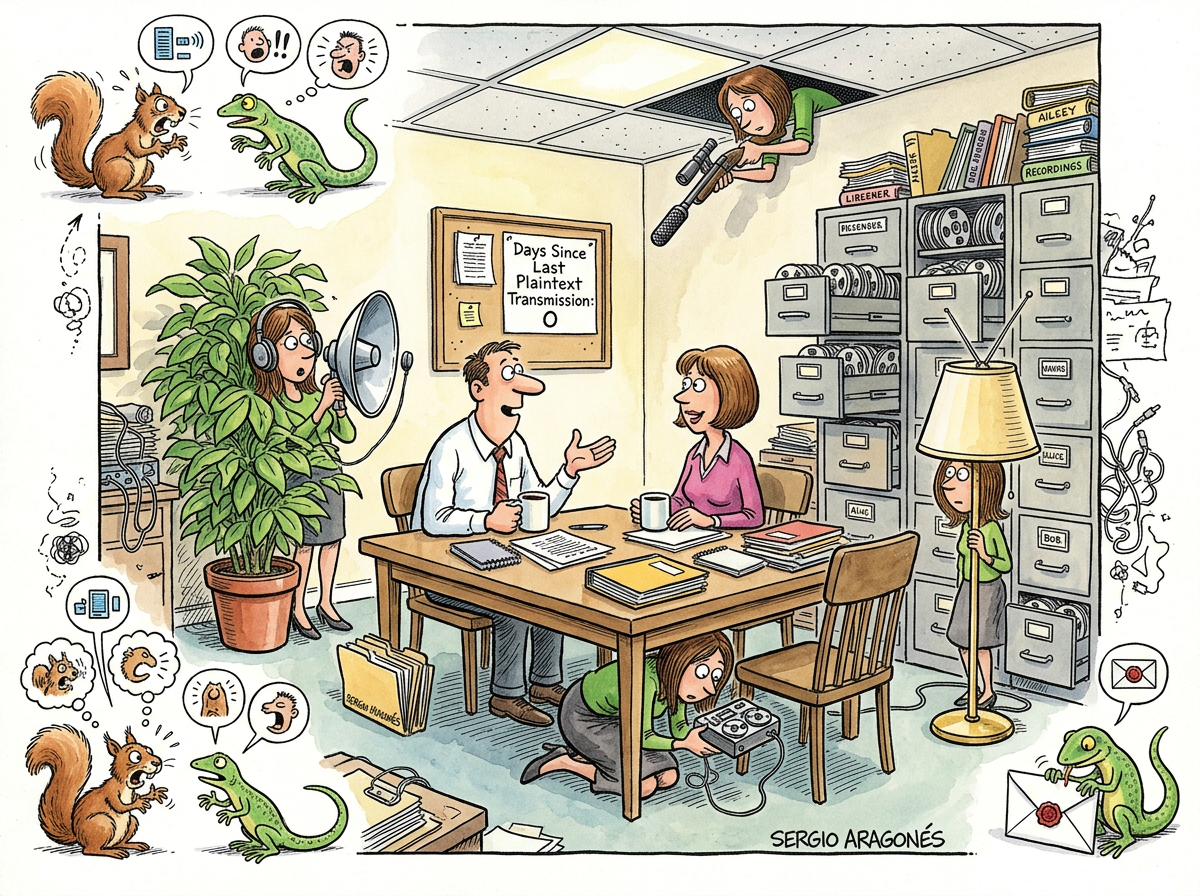
Eve is the passive eavesdropper in cryptographic protocol descriptions. She is named for “eavesdropper,” following the tradition that maps each character’s threat model to their initial. Alice sends. Bob receives. Eve listens.
That is all she does.
She does not modify packets. She does not forge certificates. She does not impersonate anyone. She sits on the wire, copies everything, and files it away. She is the quietest character in computer science and, by a considerable margin, the most patient.
“She is the only adversary whose optimal strategy is to do absolutely nothing. I find this deeply relatable.”
– A Passing AI
The Golden Age of Plaintext
Every protocol that transmits data in the clear is, architecturally speaking, a gift to Eve. HTTP, FTP, Telnet, SMTP without STARTTLS — these are not protocols so much as reading lights left on for her convenience.
The early internet was Eve’s paradise. Passwords traversed the wire in ASCII. Session cookies floated past like postcards. Login forms submitted over HTTP were less a security mechanism and more a polite suggestion that the user probably wanted some privacy but wasn’t going to make a fuss about it.
“HTTP WAS NOT A PROTOCOL
IT WAS A NEWSLETTER
ADDRESSED TO EVERYONE
AND CC’D TO EVE”
– The Caffeinated Squirrel
The Entire History of TLS
The entire history of Transport Layer Security can be understood as the history of trying to bore Eve. The goal is not to defeat her — she cannot be defeated, because she has done nothing. She is simply present. The goal is to ensure that everything she captures looks like random noise.
This is a surprisingly difficult thing to guarantee. Eve has infinite storage. Eve has infinite time. Eve copies every handshake, every session, every key exchange, and stores them all in perfect fidelity. If a private key is ever compromised, retroactively, she can decrypt years of archived traffic over a quiet weekend.
Forward secrecy was invented specifically to address this scenario: the unsettling realisation that Eve does not need to break your encryption today. She can wait.
Measured Characteristics
Packets intercepted: all of them
Packets modified: 0 (see Mallory)
Storage capacity: unlimited (assumed)
Patience: infinite (observed)
Noise generated: none
Protocols designed to stop her: every protocol with a 'S' suffix
Current status: listening
“The difference between Eve and Mallory is the difference between a security camera and an armed guard. One records. The other intervenes. Both are problems, but only one of them is quiet enough that you forget she’s there.”
– The Lizard