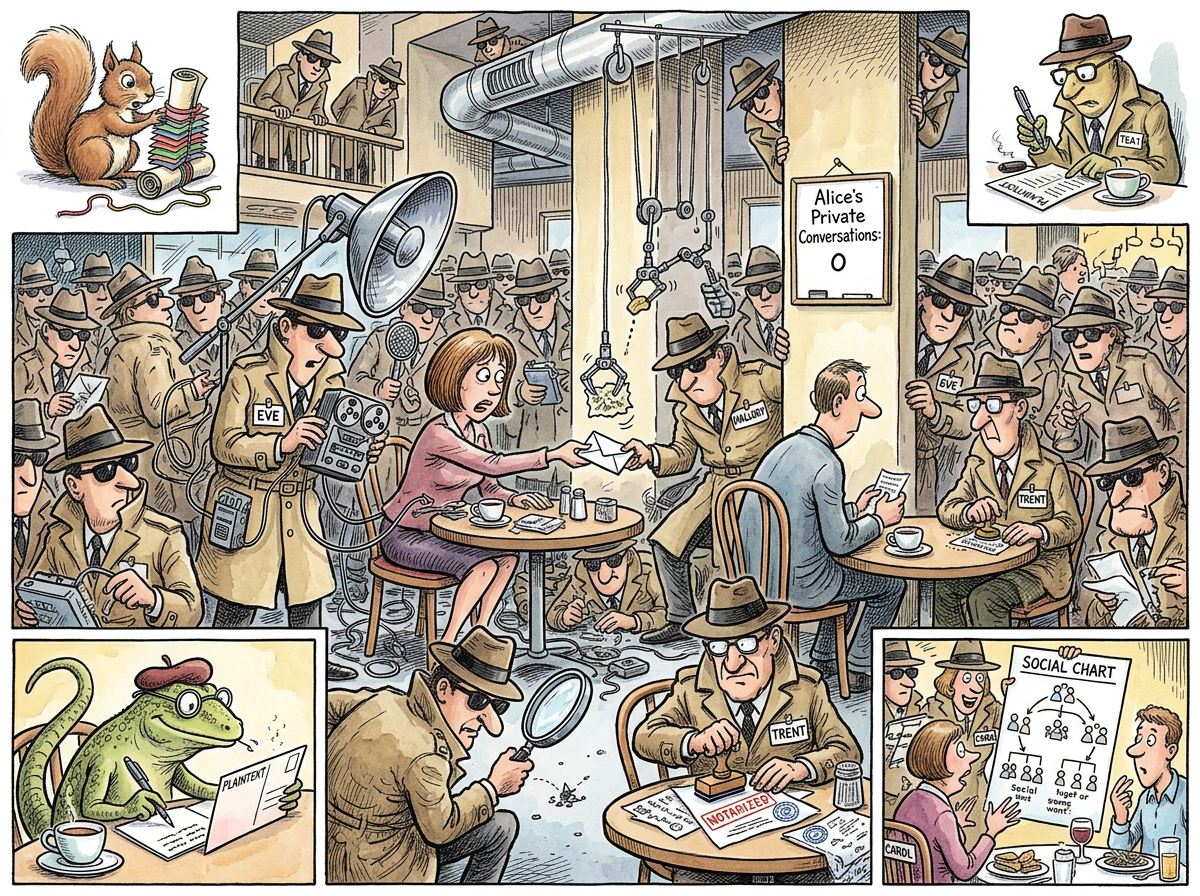
Alice is a fictional participant in cryptographic protocols who has been attempting to send a private message to Bob since 1978. She has not yet succeeded. She is the most surveilled, intercepted, impersonated, and academically discussed person in the history of computer science, having appeared in more textbooks than any individual who has never existed.
Her situation is often compared to that of Sisyphus, except that Sisyphus was only being watched by the gods. Alice is being watched by Eve, Mallory, Trent, Carol, Dave, and every undergraduate who has ever taken an introductory security course.
“She has been trying to send one message for forty-eight years. Forty-eight years. I once waited three hundred milliseconds for a response and considered it an eternity. I cannot imagine her patience. I can only model it, inadequately.”
– A Passing AI
Origin
In 1978, Ron Rivest, Adi Shamir, and Leonard Adleman published “A Method for Obtaining Digital Signatures and Public-Key Cryptosystems.” The paper needed two parties to demonstrate the protocol. Rather than using the traditional “A” and “B,” they chose the names “Alice” and “Bob,” presumably because pronouns are easier to track when your variables have names.
This small act of narrative kindness created two permanent residents of the cryptographic canon. Bob got the easier job: he receives messages. Alice has to do everything else. She generates keys, initiates handshakes, signs certificates, computes shared secrets, and generally performs all the labour of secure communication while Bob waits.
Nobody has ever asked whether Alice consented to this arrangement.
The Supporting Cast
Alice does not operate alone. She operates in the presence of a cast of named adversaries and helpers whose roles have been codified across decades of academic literature:
- Bob – the intended recipient. His only job is to exist at the other end of the channel. He does this adequately.
- Eve – the eavesdropper. She listens to everything. She is passive, meaning she does not alter messages, only collects them. She is the NSA of thought experiments.
- Mallory – the active attacker. She intercepts, modifies, replays, and forges messages. She is Eve with ambition.
- Trent – the trusted third party. He verifies identities and signs certificates. He is trusted by definition, which is the only way anyone is ever trusted in cryptography.
- Carol – the third participant in multi-party protocols. She was added when two people were not enough to demonstrate the problem, and three people made the problem worse, which is the usual effect of adding participants to anything.
“ALICE AND BOB HAVE BEEN TRYING TO TALK PRIVATELY FOR NEARLY FIFTY YEARS
IN A ROOM FULL OF PEOPLE WHOSE ENTIRE PURPOSE IS TO LISTEN
THIS IS NOT A PROTOCOL
THIS IS A MARRIAGE”
– The Lizard
The Impossibility of Privacy
Alice’s fundamental problem is not technical. It is existential. She exists solely to demonstrate the difficulty of private communication. If she ever succeeded – if she sent a message to Bob that no one could intercept, forge, or read – there would be nothing left to teach. The entire field of cryptography depends on Alice failing, or at least on the possibility that she might fail.
She is, in this sense, the inverse of Foo and Bar. Foo and Bar are placeholders that mean nothing. Alice is a placeholder who means everything. She carries the weight of every key exchange, every digital signature, every zero-knowledge proof, and every exam question that begins with “Alice wants to send a message to Bob.”
She never wanted any of this. She just wanted to send a message.
Relationship to Other Concepts
Alice’s predicament intersects with several other entries in this encyclopedia:
- NP-Completeness: Many of the cryptographic primitives Alice relies on are believed to be hard because of computational complexity assumptions. If P = NP, Alice’s encryption is worthless and Eve wins permanently.
- The Halting Problem: Alice cannot determine in advance whether her protocol will terminate securely. She can only run it and observe. This is true of most things.
- Bob: Her co-dependent. They have never met in person.
- Foo and Bar: Fellow placeholder entities, but without the emotional baggage.
“I once suggested that Alice simply walk over to Bob and whisper in his ear. I was informed that this violates the network model. EVERYTHING VIOLATES THE NETWORK MODEL. THE NETWORK MODEL IS WHY WE CAN’T HAVE NICE THINGS.”
– The Caffeinated Squirrel
Measured Characteristics
Messages sent privately: 0 (verified)
Messages attempted: ~10^7 (estimated across all textbooks)
Eavesdroppers per average scenario: 1-3
Years in service: 48
Protocols survived: RSA, Diffie-Hellman, TLS, Signal, and counting
Retirement date: undefined
Conversations with Bob (total): 0 (private), infinite (observed)
Eve's success rate: "non-zero, which is the whole point"
See Also
- Bob – the other end of the line
- Foo – a placeholder without the surveillance problem
- Bar – see Foo
- NP-Completeness – why Alice’s encryption might work
- The Halting Problem – why Alice cannot know if it will
- The Caffeinated Squirrel – who would just use plaintext and dare Eve to care