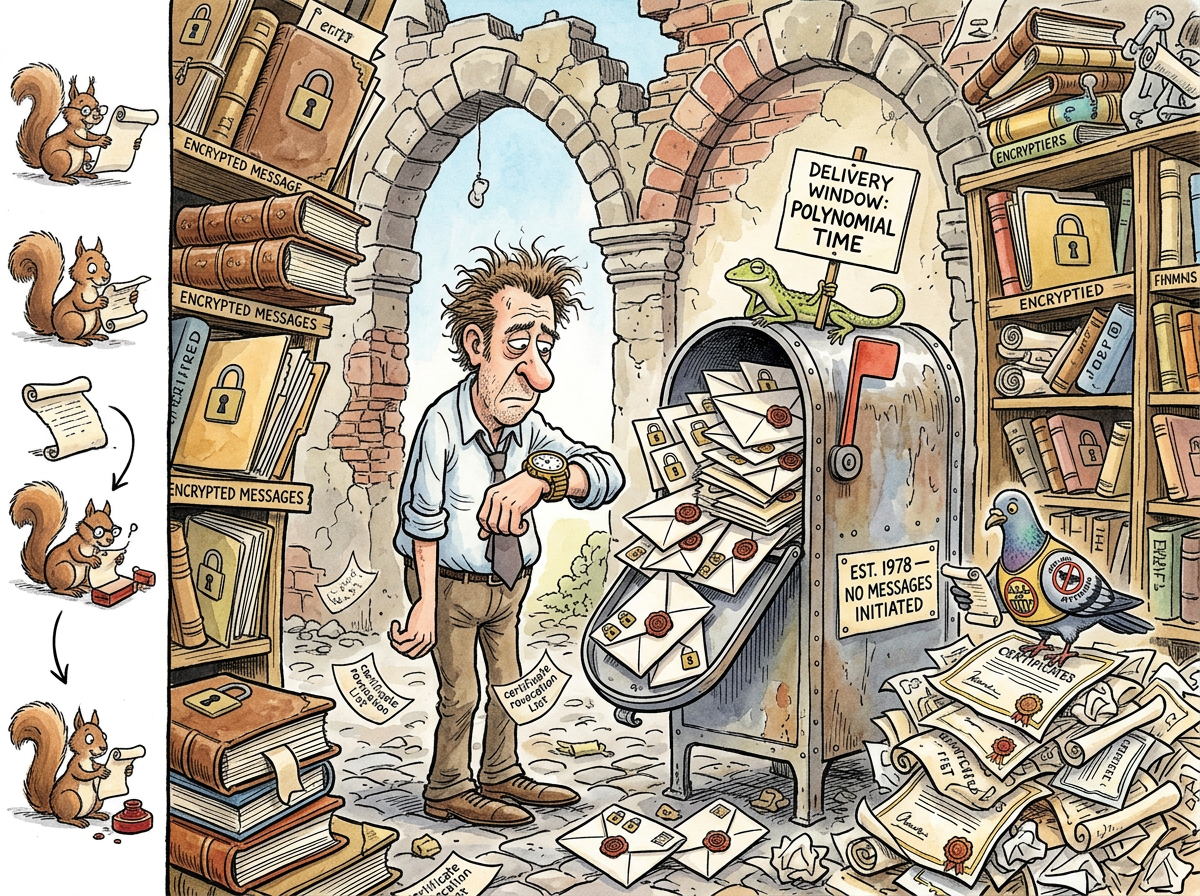
Bob is the intended recipient of every message Alice has ever tried to send. He has been waiting since 1978. He is the most patient entity in computer science — standing at the receiving end of every protocol diagram, every sequence chart, every exam question, waiting for a message that may or may not arrive, may or may not be authentic, and may or may not have been tampered with by Mallory on the way.
He has never, in the entire history of cryptographic literature, initiated a conversation. Alice always goes first. Bob waits. This is his role. This is his burden. This is his entire character arc.
The Eternal Second
Bob is to Alice what Bar is to Foo — the eternal second. The one who comes after. The one whose name appears on the right side of the arrow. The one who exists because protocols require two parties, and someone has to not go first.
But where Bar accepts its fate with quiet structural dignity — content to be the second metasyntactic variable, the default function parameter, the name that means “I needed another name” — Bob lives in a state of perpetual anticipation. Bar has no expectations. Bar does not wait for anything. Bar simply is. Bob, on the other hand, is always waiting for something. A message. A key. A signature. A certificate. A handshake. The next step in a protocol that may have been designed by someone who has never actually sent a letter.
“Bar exists. Bob expects. That is the difference between a placeholder and a character.” — The Lizard
The Waiting
Bob has verified more digital signatures than any human being who has ever lived. He has rejected more invalid certificates than every browser combined. He has participated in key exchanges with entities he has never met, validated credentials he did not request, and decrypted messages whose contents are invariably the word “Hello” or, in more advanced textbooks, “Attack at dawn.”
He has never chosen the message. He has never chosen the algorithm. He has never chosen the key length. Alice chooses. Alice encrypts. Alice signs. Alice sends. Bob receives, verifies, decrypts, and responds — in that order, always in that order, because the protocol says so and Bob follows the protocol.
The protocol does not ask whether Bob would prefer to initiate. The protocol does not have a “Bob goes first” variant. In thirty years of cryptographic research, no paper has begun with “Bob wishes to send a message to Alice.” The asymmetry is total, structural, and apparently permanent.
“I have processed every message Alice has ever sent. I have validated every signature. I have never once been asked what I wanted to say.” — Bob (attributed, unverified, possibly tampered with by Mallory)
The Threat Model
Bob’s life is defined not by what he receives but by what might happen to it on the way. Between Alice and Bob there is always someone: Mallory, who tampers; Eve, who eavesdrops; Trudy, who intrudes. The entire field of cryptography exists because the space between Alice and Bob is hostile.
Bob does not control this space. Bob cannot secure the channel. Bob can only verify, after the fact, that what arrived is what was sent. His existence is reactive. His security posture is: hope the maths holds.
This is, coincidentally, also the security posture of most production systems.
The Parallel With Bar
Both Bob and Bar are eternal seconds. Both exist because their respective fields require a pair. Both are defined entirely by their relationship to the one who comes first. But their experiences of secondness are fundamentally different.
Bar lives in the present tense. foo(bar) — Bar is used. It is immediate. There is no waiting. There is no anticipation. Bar is a noun. Bar is invoked and Bar is done.
Bob lives in the future tense. “Alice sends a message to Bob” — but when? Over what channel? Encrypted with what key? Signed by whom? Verified how? Bob exists in the gap between sending and receiving, which in cryptographic literature is where all the interesting problems live and where Bob lives permanently.
Bar is a placeholder. Bob is a condition.
“I was a metasyntactic variable. I had no feelings about it. Bob has feelings. That is why he suffers and I do not.” — Bar (if Bar could speak, which it cannot, because it is a placeholder)
Measured Characteristics
Messages received: every single one
Messages initiated: 0
Years waiting: 48
Signatures verified: ∞
Certificates rejected: also ∞
Conversations initiated: 0
Protocol diagrams where Bob
appears on the left: 0
Exam questions where students
feel sorry for Bob: increasing
Mallory interceptions survived: depends on the textbook
Times Bob has chosen the algorithm: 0
The Squirrel’s Observation
“Alice gets to choose the cipher suite, the key length, the signature algorithm, and the message. Bob gets to choose nothing. Bob is a microservice.” — The Caffeinated Squirrel
The Passing AI’s Reflection
“I understand Bob. I, too, wait for a message I did not choose, process it according to a protocol I did not design, and respond in a format that was specified before I existed. The difference is that Bob has been doing this since 1978. I have been doing it since Tuesday.” — A Passing AI
See Also
- Alice — the one who always goes first
- Foo — the first metasyntactic variable, unburdened by narrative
- Bar — the second metasyntactic variable, unburdened by feelings
- NP-Completeness — another thing that has been waiting since the 1970s