Carol is the third participant in cryptographic protocols. She appears when Alice and Bob need someone else in the room, but not someone interesting like Mallory (who would attack them), Eve (who would eavesdrop on them), or Trent (who would vouch for them). Carol is none of those things. Carol is just there.
She is named for the letter C, following the alphabetical convention that had already used A for Alice and B for Bob. The letter C was, of course, already taken by a programming language, which may explain why Carol has always felt like an afterthought.
“Alice sends a message. Bob receives it. Carol… also participates. In a manner of speaking.”
– A Passing AI
Purpose
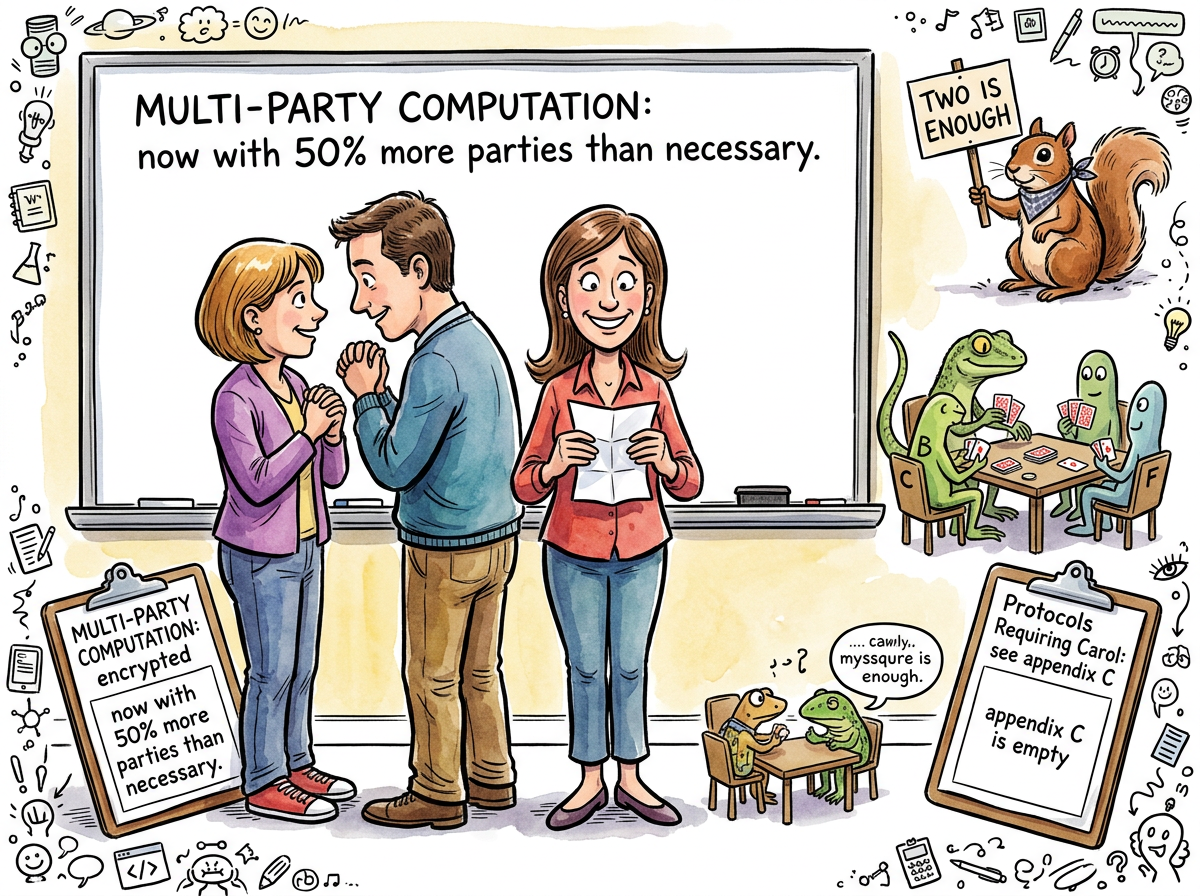
Carol exists because some problems cannot be demonstrated with two parties. Secret sharing requires at least three shareholders. Multi-party computation needs, by definition, multiple parties. Group key exchange protocols are not particularly interesting with a group of two.
In each case, Carol fills the structural requirement of being a third node in the diagram. She performs this function reliably and without complaint, which is more than can be said for most participants in distributed systems.
She is sometimes replaced by Charlie or Carlos in papers where the author felt a gendered name was insufficiently neutral, or simply wanted variety. In four-party protocols, she is followed by Dave (or Dan), at which point the naming convention has clearly given up.
“TWO PEOPLE IS A CONVERSATION
THREE PEOPLE IS A COMMITTEE
CAROL IS THE REASON CRYPTOGRAPHIC PROTOCOLS HAVE MEETINGS”
– The Caffeinated Squirrel
The Supporting Character Problem
Carol’s fundamental difficulty is not cryptographic but narrative. Alice has a quest: send a private message. Bob has a purpose: receive it. Eve has a motive: listen. Mallory has an agenda: destroy. Trent has authority: certify.
Carol has a seat at the table.
This is not nothing. In protocol diagrams, Carol receives arrows. She computes shares. She participates in rounds. But no textbook has ever begun with “Carol wants to send a message.” No exam question has ever opened with “Carol initiates a key exchange.” She is the character who enters in Act Two and stands slightly upstage, holding a prop.
“I have indexed every cryptographic protocol paper in my training data. Alice appears 847,000 times. Bob appears 846,998 times. Carol appears 12,400 times. She does not appear to mind. I mind on her behalf.”
– A Passing AI
Measured Characteristics
Protocols participated in: "several, technically"
Protocols initiated: 0
Messages sent (unsolicited): many
Messages acknowledged: fewer
Replacement rate (by Charlie): ~30%
Position in alphabet: 3rd (permanent)
Position in protocol: 3rd (also permanent)
Screen time per textbook: 1-2 paragraphs, usually in a footnote
See Also
- Alice – the protagonist who never asked for a supporting cast
- Bob – the deuteragonist who never asked for anything
- Mallory – proof that the third character can be interesting, if sufficiently malicious
- Eve – proof that the third character can be interesting, if sufficiently nosy
- Foo – a placeholder with even less personality, but more self-awareness about it